Top Notch Tips About How To Build An Enterprise Network
This is why it’s good.
How to build an enterprise network. To build a professional network, start by setting networking goals. The real work is in maintaining your network and investing in the relationships beyond the first encounter. Focus on finance from the very beginning:
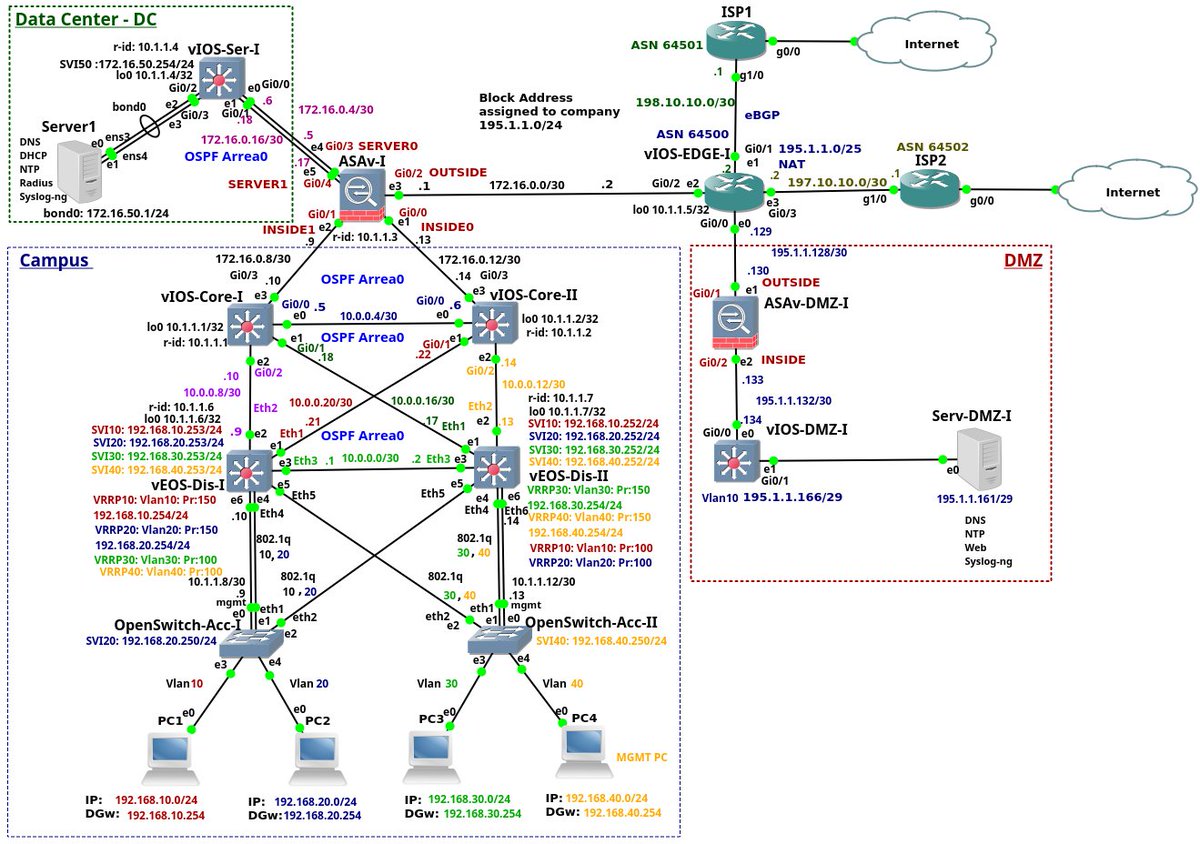
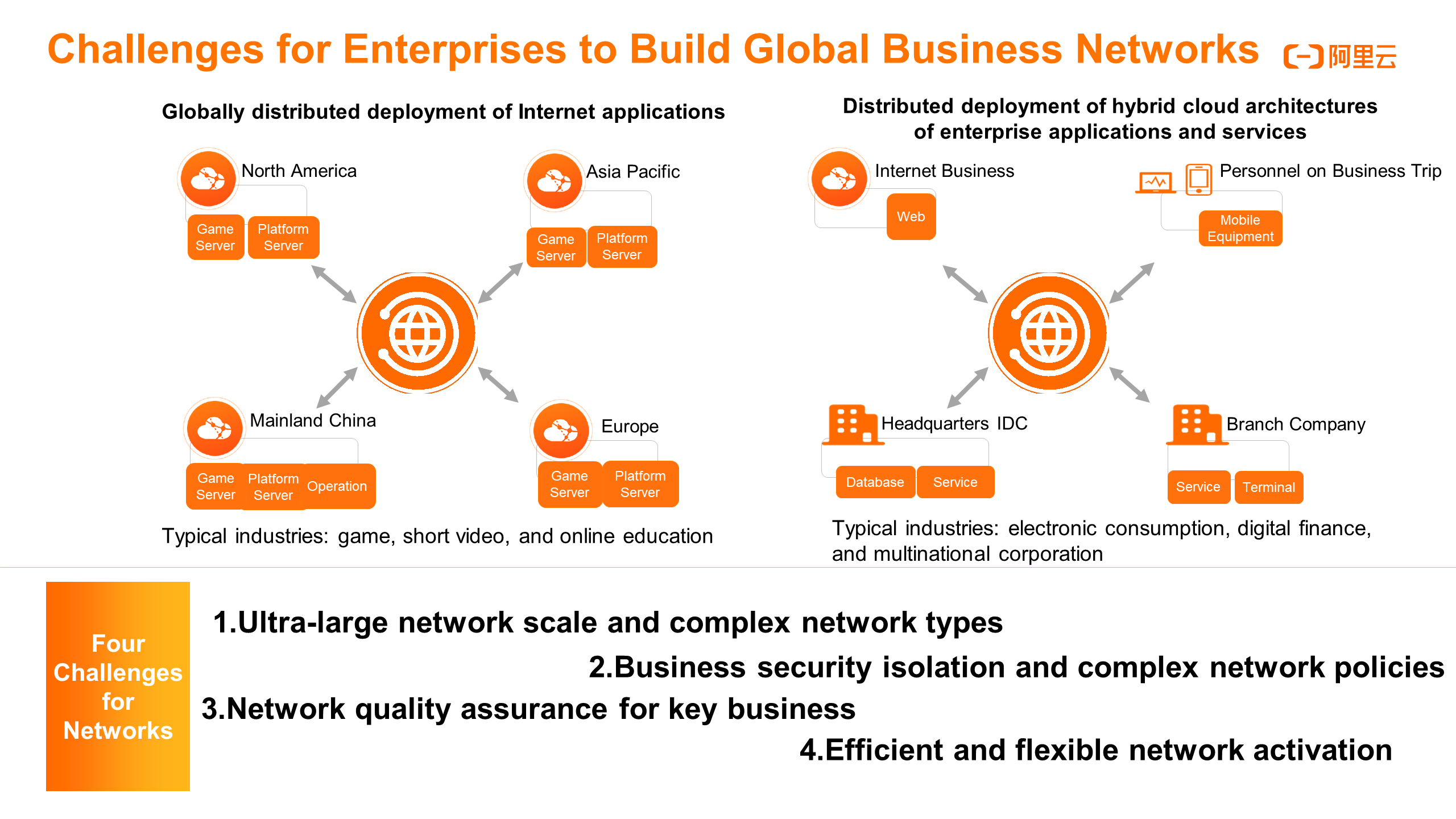
Ad explore 8 issues it professionals keep facing & discover the solutions to remedy them. Nutanix provides cloud connectors to aws, microsoft azure and google cloud. The complexity of new enterprise architectures will drive enterprises to invest heavily in the security of the network edge.
Select and deploy edge computing solutions. Before you can understand your cyber threat landscape, you need. Decide whether you want to build a dedicated 5g network or buy space on an existing carrier’s network.
Then start putting yourself out there. The following are several tips to consider to get started building your professional network: Edge computing companies are the vendors offering organizations the hardware, networking machinery, processors, colocation.
Here are some of my top tips i would share with younger entrepreneurs just starting out: Understand your cyber threat landscape. Determine whether your enterprise needs its own 5g network.
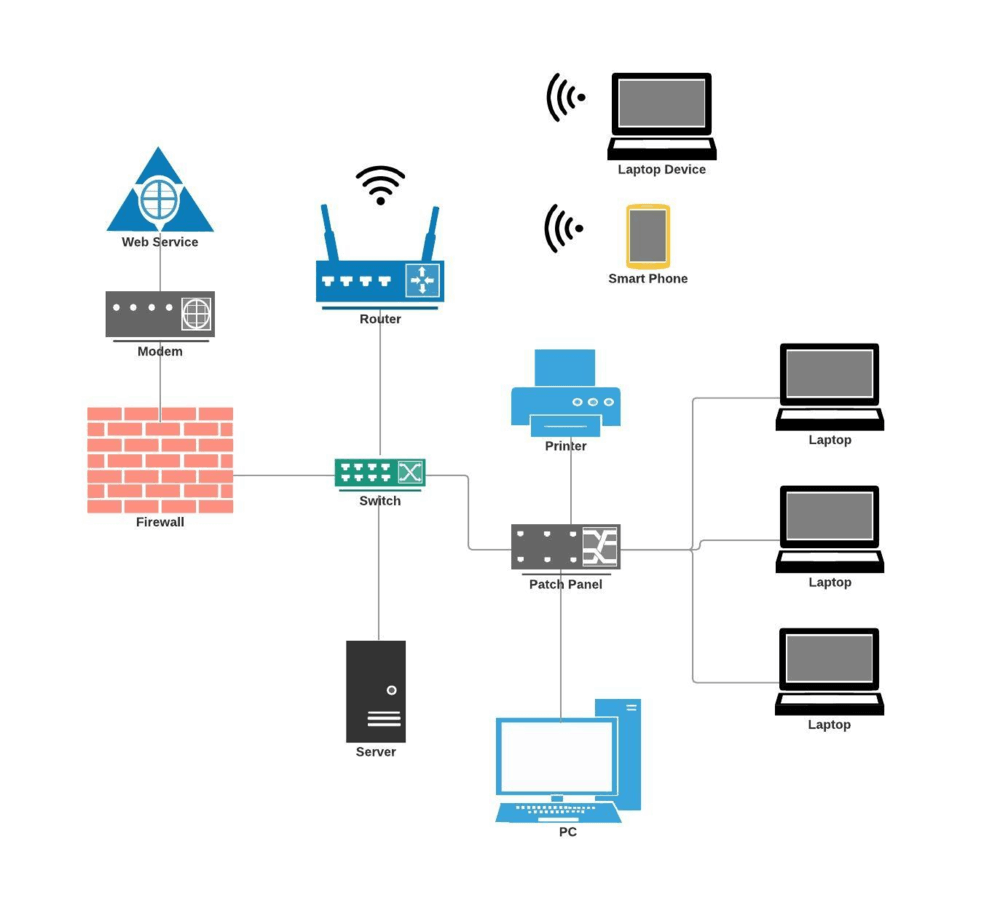
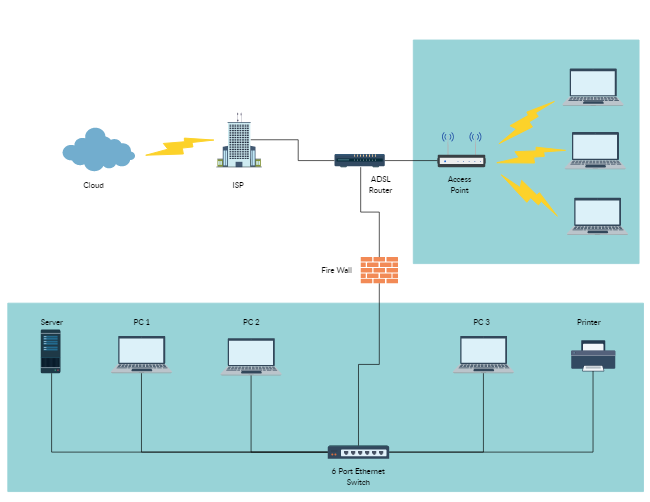
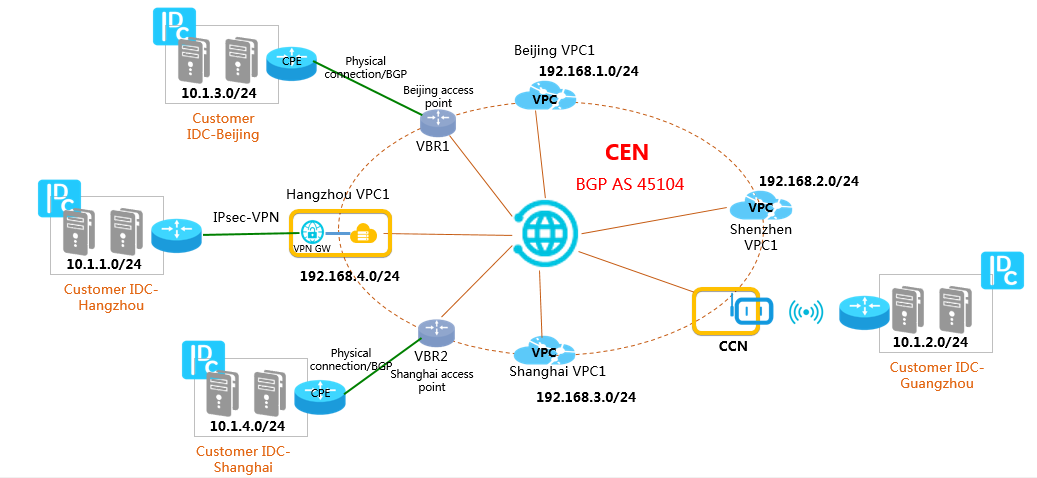
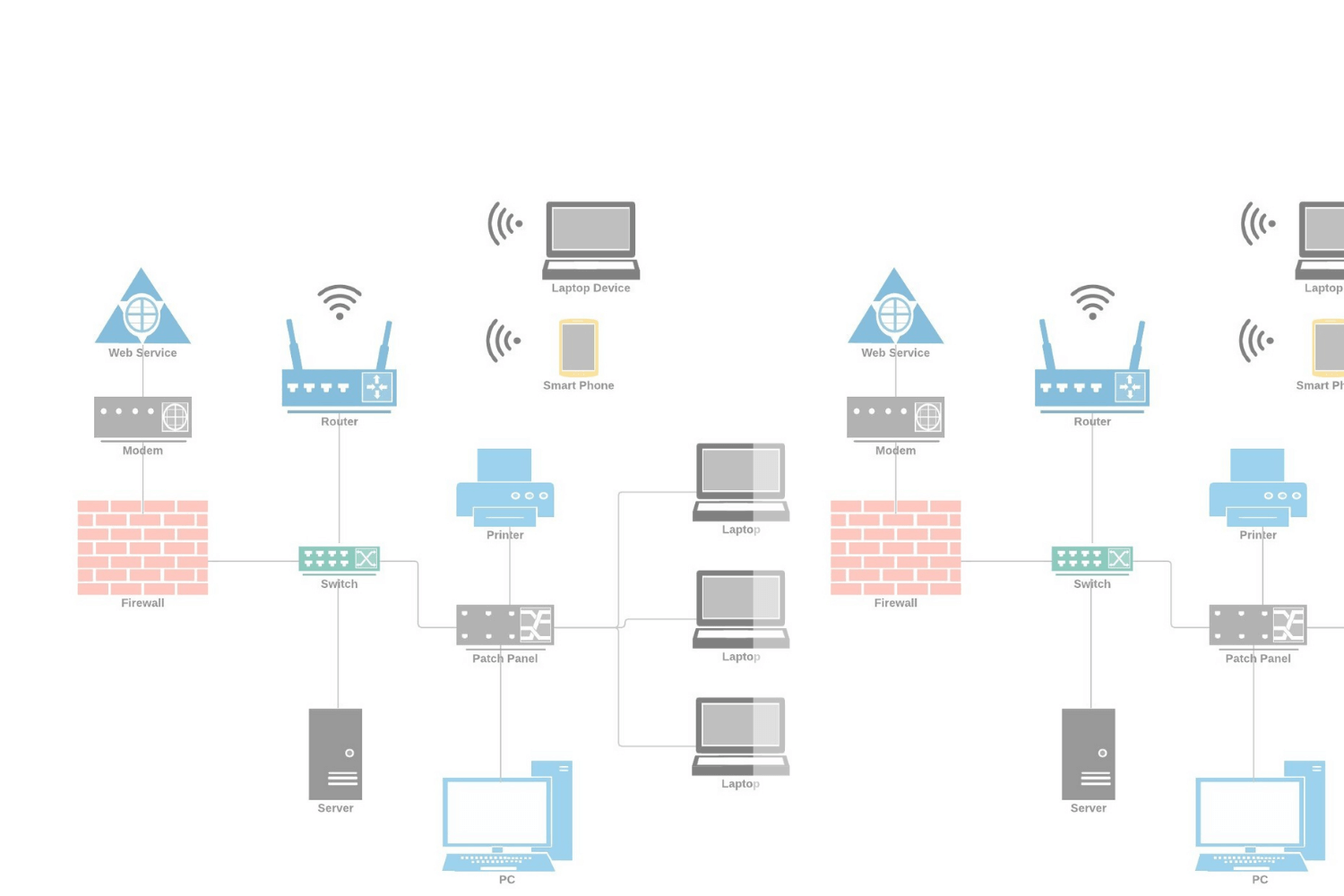
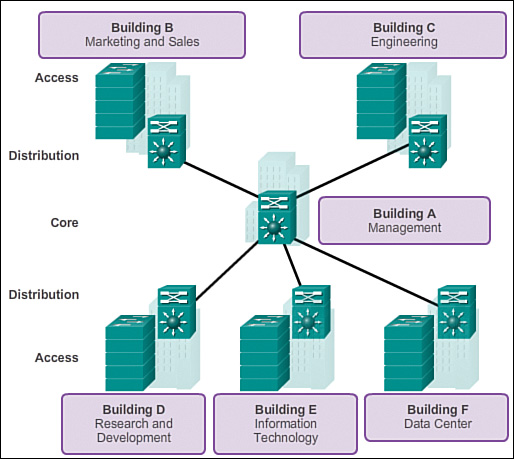
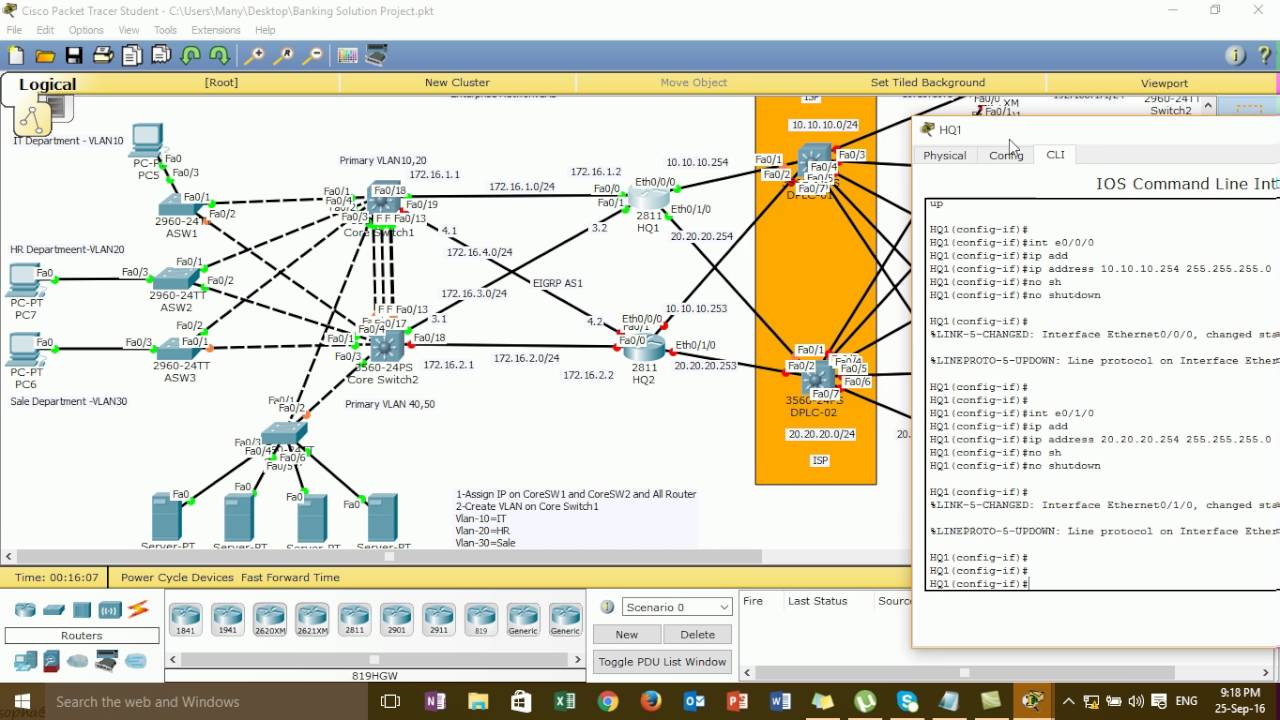
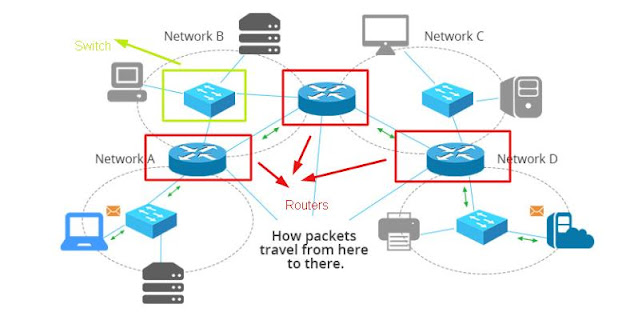
Have a clear vision of the financial. Here are the basic steps to follow developing an effective security strategy. An enterprise network is a hardware and software infrastructure that connects a company’s computers, servers and other devices.
In this guide, we will provide 12 steps on how to secure your business network starting today. Reach out to current connections, join local and national. Those critical features of your network are your “protect surface”.
How to take the sh out of it Send your iot data to public cloud services. Once you get started, building your network is actually the easy bit.
It allows employees to connect to shared. Security is a blackhole it sucks money in but if it does what it is. Search for people who can make a difference.
You can’t very well tighten and improve network security without first. When establishing your zero trust protocols, it is important to look beyond the greater attack surface.